Oracle Maximum Security Architecture
16. 2. 2023

We participated on Oracle Conference in Kosice on 09. February. Nowadays, when data is valueable asset for many companies, data security is the most important topic. This blog deals with Oracle Oracle maximum security arichtecture as a complex solution for data security.
Nowadays, for many companies, data is their greatest asset for competition and differentiation. As the most valuable property it yields to subject of loss, theft, espionage etc. Companies are then challenged to protect their growing volume of data from increasing security threats that could endanger their profits.
In this case, risk is a product of
- threat, what can happen,
- value of data being lost or misused,
- vulnerability corresponds to the level of security
- impact that must be taken to revert original state.
Companies’ executives must admit that it can happen, it can even ruin the company, if they are not prepared and sufficiently and continuously secured. To reduce that risk, companies MUST priorities data security. Todays, data as a subject of theft or misusage can be also subject of insurance. To insure data, companies must adapt and implement required security architecture. This can be more cost consuming for the solutions on-Premise. With migrating into Oracle cloud and modern OCI architecture security. Here are some facts regarding annual grow of escalating cybercrime.

Company needs to guard that data with security controls that restricts access. Oracle provides industry-leading capabilities for each of these security control objectives.
- Assess the system to determine its current state and develop a remediation plan
- Detect attempts to access data outside of policy and identify anomalies in data
- Prevent access to data that doesn’t go through the database control mechanisms
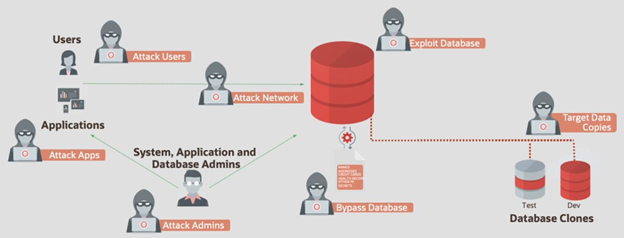
How are databases attacked?
Ransomware: The cybersecurity threat most IT directors fear
- More than 4,000 attacks per day
- US organizations lost more than $10 billion in 2020
- 19-day average downtime
- Average total cost per breach: $3.86M
- Cost of one lost record: $150
- Average size of data breach: 25,575 records
- Average total remediation cost $1.85M
Top 9 threats
- Ransomware
- Malware
- Cryptojacking
- E-mail related threats
- Threats against data; (this category encompasses data breaches/leaks)
- Threats against availability and integrity
- Disinformation – misinformation
- Non-malicious threats; (mostly based on human errors and system misconfigurations)
- Supply-chain attacks
Well known cases:
- Equifax, in 2017, loss of 147Mil customer records in value of 1 billion USD
- Capital One, loss of 100 million customer data, penalty of 80 million USD.
Maximum Security Architecture
Oracle propsed and designed Maximum Security Architecture, as shown on next picture. Most of the features of the database depicted below are available to any Enterprise Edition customer. A few are extra-cost options or products.
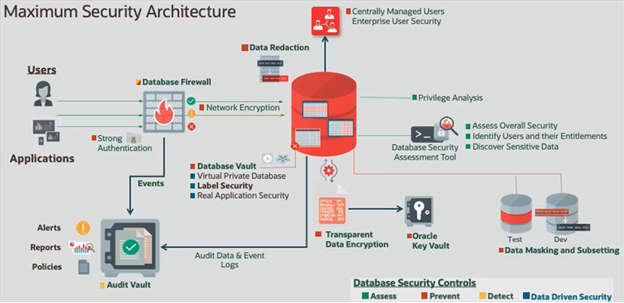
Firstly, users should authenticate with something stronger than password – the Oracle Database supports Radius, Kerberos, and PKI certificate authentication. Use database security assessment tool (DBSAT) to assess the database configuration and identify deviations from best practices. If the database is configured poorly, then other controls may not be effective. For more info see here.
Because data are stored on disks, using backups and exports are protected from attack there. Here is Transparent Data Encryption (TDE), part of Oracle Advanced Security comes into usage. TDE encrypts data on the operating system, in storage devices, in backup and export files.
After data is encrypted, encryption keys need to be protected and distributed securely. For this Oracle Key Vault (OKV) is used. Oracle Database Vault implements data security controls within Oracle Database to restrict access to application data by privileged users.
Database Firewall, part of Oracle Audit Vault and Database Firewall, is used to check incoming connections and SQL statements.
For more detailed information see primer on database security.
Executives must take into account the fact, that when running oracle database on premise, the maximum-security architecture should be implemented locally and keep up-to-date any time.
Maximum Security Architecture in the Cloud
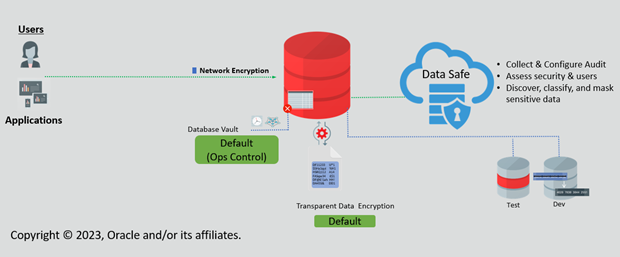
Maximum Security Architecture is even easier in the cloud.
Database running in the Oracle Cloud has Oracle Data Safe immediately and fully available. Data Safe provides several features to help you secure your Oracle Databases, and can take the place of DBSAT, Audit Vault, and Data Masking.
Other options like Database Vault and Transparent Data Encryption are also available for you in the cloud, and for most cloud services (like Oracle Autonomous Database), are included in your subscription at no additional charge.
CCW as Oracle partner can help you to increase your security with migrating into the cloud. For any more information please contact us.
Späť na Blog